Configuring Exchange On-Premise
This guide explains how to configure the Nextcloud Exchange Connector to authenticate with Microsoft Exchange On-Premise environments (Exchange 2016, Exchange 2019).
Note:
Unlike Microsoft 365 Cloud environments that use OAuth app registrations, On-Premise setups rely on dedicated Service Accounts. To securely synchronize calendars and contacts without knowing every user's personal password, the connector utilizes the ApplicationImpersonation role in Exchange.
Pre-requirements
Before you begin configuring the Exchange Server, ensure you have the following:
Administrative Access: You must have access to the Exchange Admin Center (EAC) with an account that holds "Organization Management" or "Role Management" permissions.
Exchange Web Services (EWS): EWS must be enabled and externally accessible if your Nextcloud instance is hosted outside your local network.
Step 1. Create Exchange Service Accounts
Why this is needed: You must create dedicated user accounts in your Active Directory/Exchange environment that the connector will use to act as a background daemon.
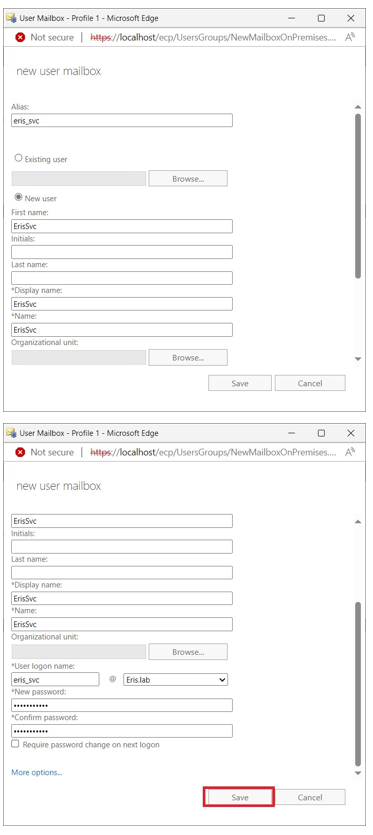
Open your Active Directory Users and Computers (ADUC) or Exchange Admin Center.
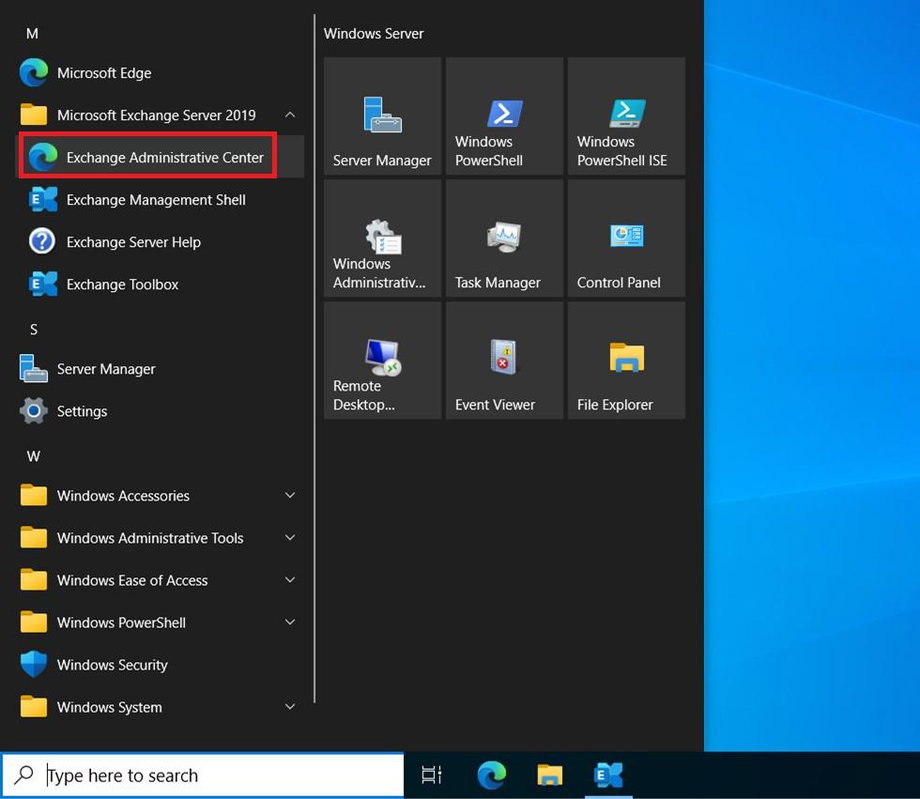
Login as an Administrator.
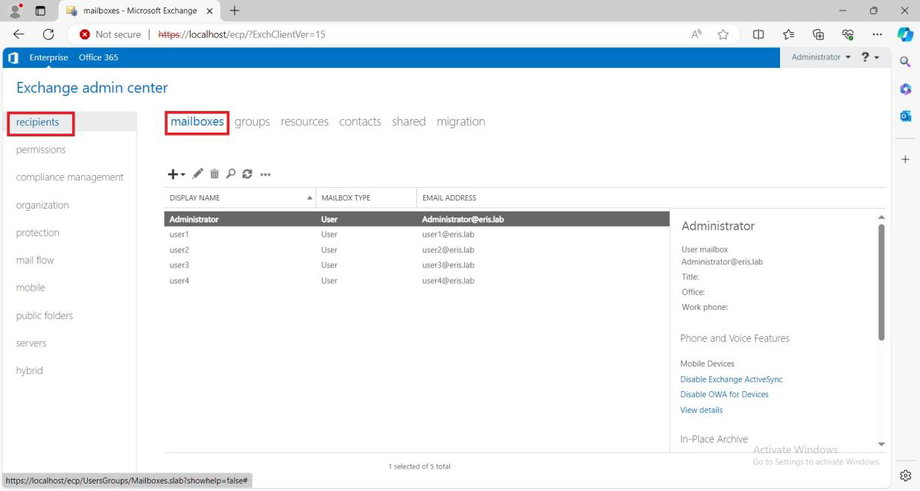
In the left-hand sidebar, select recipients.
Select mailboxes.
Select '+' → User mailbox.
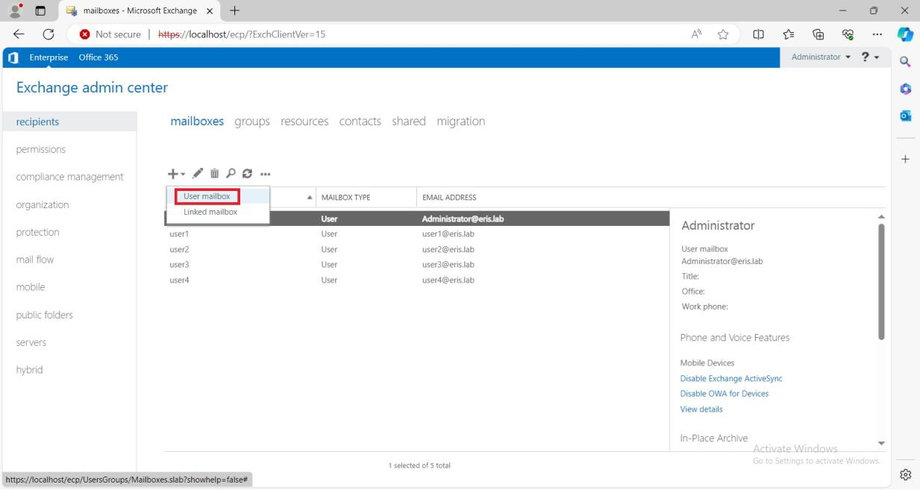
Fill in the required fields and press Save.
Pro Tip: Bypass Exchange Throttling
Microsoft Exchange enforces strict throttling limits on concurrent EWS connections per user account. If you are synchronizing hundreds or thousands of users, a single service account will quickly hit this limit, causing synchronization to bottleneck.
We highly recommend creating multiple service accounts (e.g., sync-admin-1, sync-admin-2) from the start. The connector will distribute the load across them automatically.
Step 2. Configure the Impersonation Role Group
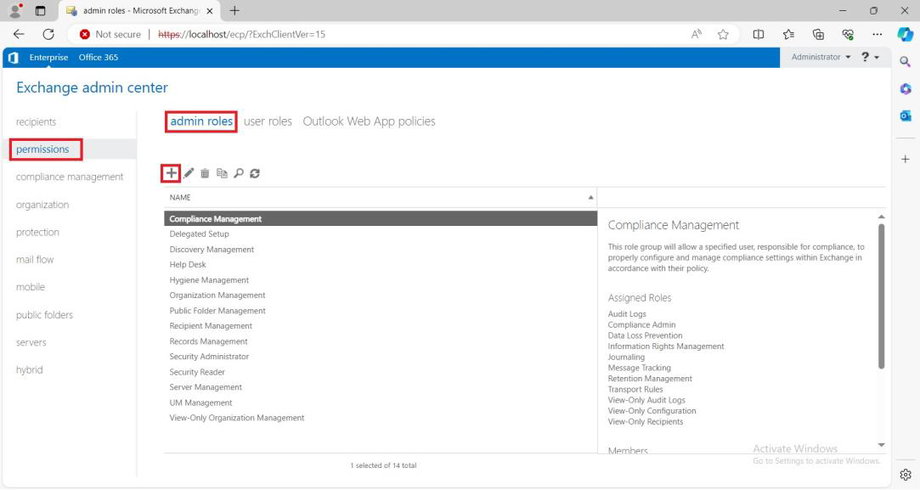
In the left-hand navigation pane, navigate to permissions and select the admin roles tab.
Click the + (Add) icon to create a new role group.
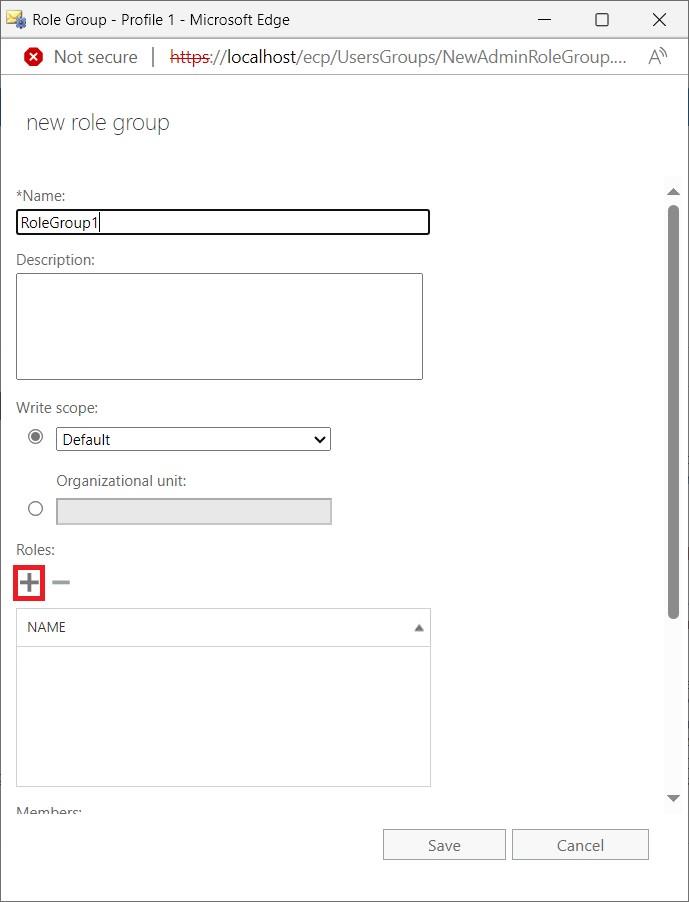
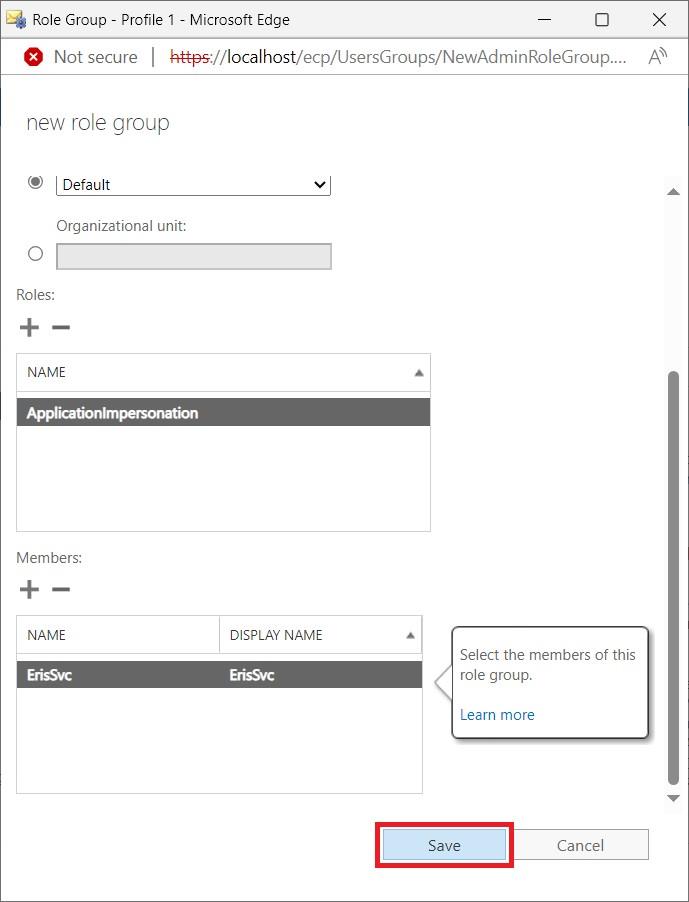
In the new window, enter a descriptive Name (e.g.,
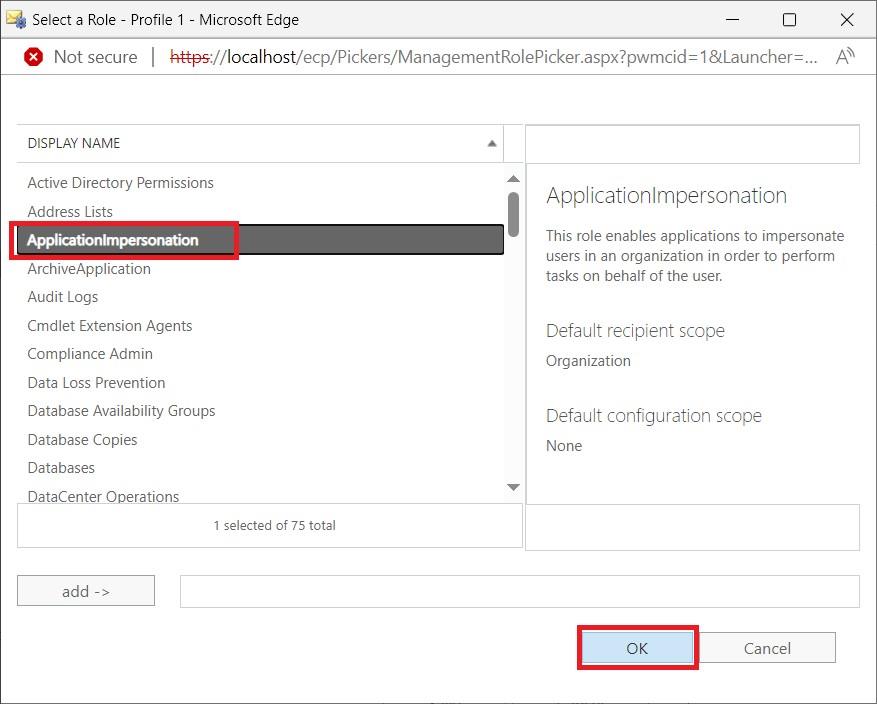
Nextcloud Sync Impersonation) and an optional description.Scroll down to the Roles section and click the + (Add) icon.
Step 3. Assign Service Accounts to the Role Group
Still inside your newly created Role Group window, scroll down to the Members section.
Click the + (Add) icon.
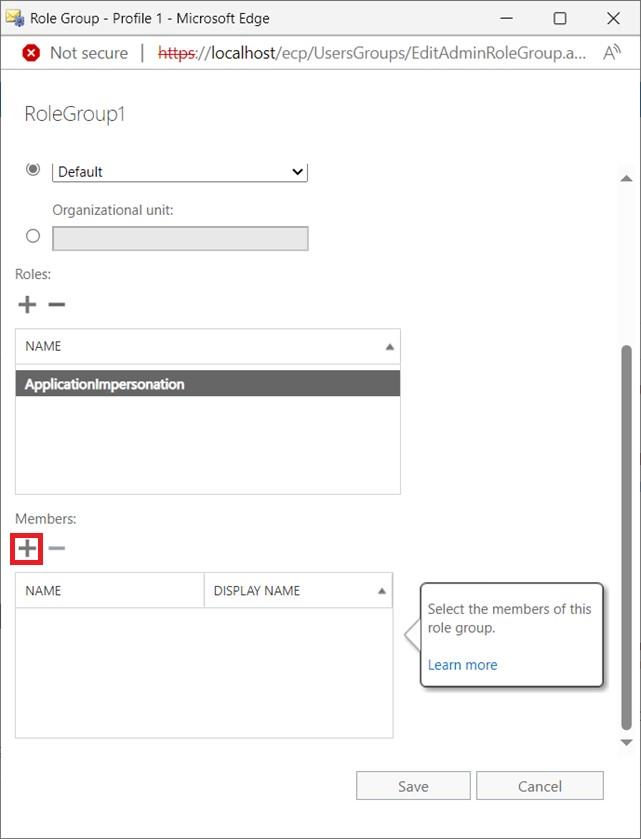
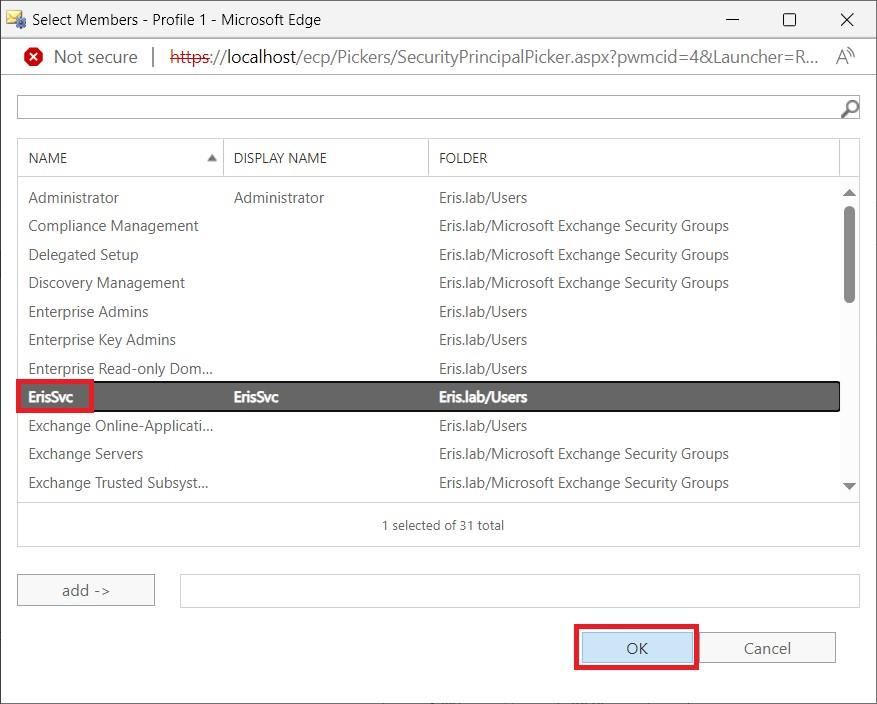
Search for and select the service accounts you created in Step 1.
Click add -> and then click OK.
Click Save to create the Role Group and apply the permissions. It may take a few minutes for the permissions to fully propagate across your Exchange environment.
Step 4. Save Credentials for Installation
You have successfully prepared your Exchange environment. Keep these credentials secure. Later, when you reach the Installation Guide, you will use these values to build your configuration files.
Configuration mapping cheat sheet
1. The .env Configuration File
When configuring your .env file, ensure you set the correct On-Premise Exchange Type (2 for Kerberos, 3 for Basic Auth, or 4 for ADFS). You must also provide your EWS endpoint URL and domain:
# Allowed Exchange Types: OnPremKerberos(2), OnPremBasicAuth(3), OnPremADFS(4)Service__ExchangeConfiguration__ExchangeType=2 # The URL to your EWS endpointService__ExchangeConfiguration__ExchangeOnPremUrl=https://exchange.example.com/EWS/Exchange.asmx # The domain of your service accountsService__ExchangeConfiguration__ExchangeOnPremDomain=your_domain_here2. The admins.json Credentials File
When building your admins.json file inside the exchangeAdmins directory, format your array based on your authentication type.
For Kerberos (2) and BasicAuth (3):
[ { "Username": "sendent-sync-1", "Password": "SecurePassword1!" }, { "Username": "sendent-sync-2", "Password": "SecurePassword2!" }]For ADFS (4):
[ { "ClientId": "your-adfs-client-id-1", "ClientSecret": "your-adfs-client-secret-1" }]